DNS Resolution issue with my domain name on new Omada environment
I’m running into a very odd DNS resolution issue after migrating from a Ubiquiti (UBNT) environment to TP-Link Omada. Everything worked perfectly before, so this appears to be Omada-related. I’m hoping someone here has run into something similar.
Environment
- Omada router: ER8411 v1.0 (1.3.6)
- Controller: OC200 v2.0 (2.24.6)
- Switch: SG2210P v5.20 (5.20.20)
- Access points: EAP772 v2.0 (1.3.14)
- Pi-hole (DNS): 10.0.5.20
- Internal web server (Apache reverse proxy with ACLs): 10.1.5.3
- Multiple VLANs (management, main, server, etc.)
DNS Configuration
- DNS Proxy: disabled
- Omada local DNS entry:
mydomain[.]com → 10.1.5.3 - Pi-hole also has:
mydomain[.]com → 10.1.5.3 - DHCP:
- Some VLANs use Pi-hole (10.0.5.20)
- Others use default gateway DNS
- Behavior is the same regardless of which DNS server is assigned
- Querying either the gateway or Pi-hole produces the same incorrect result
- OpenVPN is configured on the Omada router, with DNS set to Pi-hole
Goal
I want split DNS behavior:
- External:
mydomain[.]com → public IP (working correctly) - Internal:
mydomain[.]com → 10.1.5.3 (NOT working)
Current Behavior
- Internal DNS queries for mydomain[.]com return the IP of the Omada device the client is connected through.
Examples:
- Connected to AP1 (10.0.0.10) → DNS returns 10.0.0.10
- Connected to AP2 (10.0.0.11) → DNS returns 10.0.0.11
- Wired to switch (10.0.0.3) → DNS returns 10.0.0.3
Important notes:
- The DNS server being queried is still Pi-hole or the gateway depending on what vlan the device is on
- If I query Pi-hole locally from itself, it returns the correct IP (10.1.5.3) ... So Pi-hole appears to be functioning correctly
Additional observations:
- OpenVPN clients resolve perfectly (must be connected from outside the network obviously)
- External resolution works correctly (public IP returned)
- All internal and external subdomains resolve correctly (e.g. homeassistant[.]mydomain[.]com)
- Only the root domain (mydomain[.]com) is affected
What I’ve Tried
- Switching DHCP DNS between Pi-hole and gateway (ddefault setting)
- Adding and removing local DNS entries in Omada
- Letting Pi-hole handle DNS entirely everywhere or not at all anywhere
- Enabling and disabling DNS proxy override (proxy to the pihole when on)
- Removing all ACLs (currently none configured until this issue is sorted out)
- Testing with no local DNS / dns proxy / DHCP DNS settings at all
Current Theory
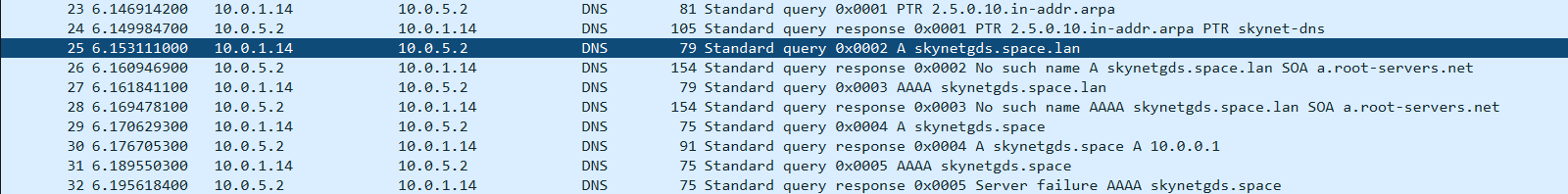
It seems like Omada (likely the APs or switch) is intercepting DNS queries and somehow rewriting responses for the root domain only. I cannot explain why it would behave this way or why only the base domain is affected.
Questions
- Has anyone seen Omada return device IPs in DNS responses like this?
- Is there any kind of DNS interception, captive portal, or “optimization” feature that could cause this?
- Why would this affect only the root domain and not subdomains?
- How can I resolve this issue? Our current workaround is super ugly (disconnect phone from wireless, turn on hot spot, connect laptop to hot spot, and VPN into local network with openVPN.
Any guidance would be GREATLY appreciated…