vlan isolation
vlan isolation
I'm struggling with gateway, switch and eap type of acl rules.
I'm trying to find a way of isolating 2 vlans from the rest.
Meaning only internet traffic is allowed for these 2 vlans.
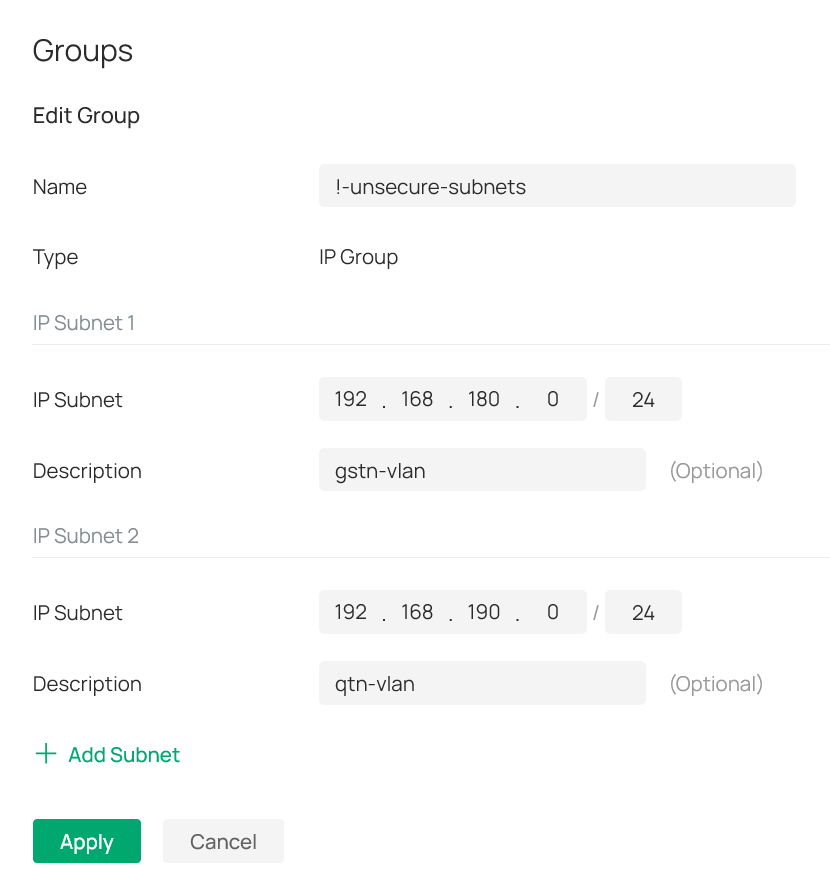
For that I have created 2 ip-groups (see attached pictures).
One has the 2 subnets I'm trying to isolate ( labeled as !-unsecure-subnets): 192.168.180.0/24 and 192.168.190.0/24.
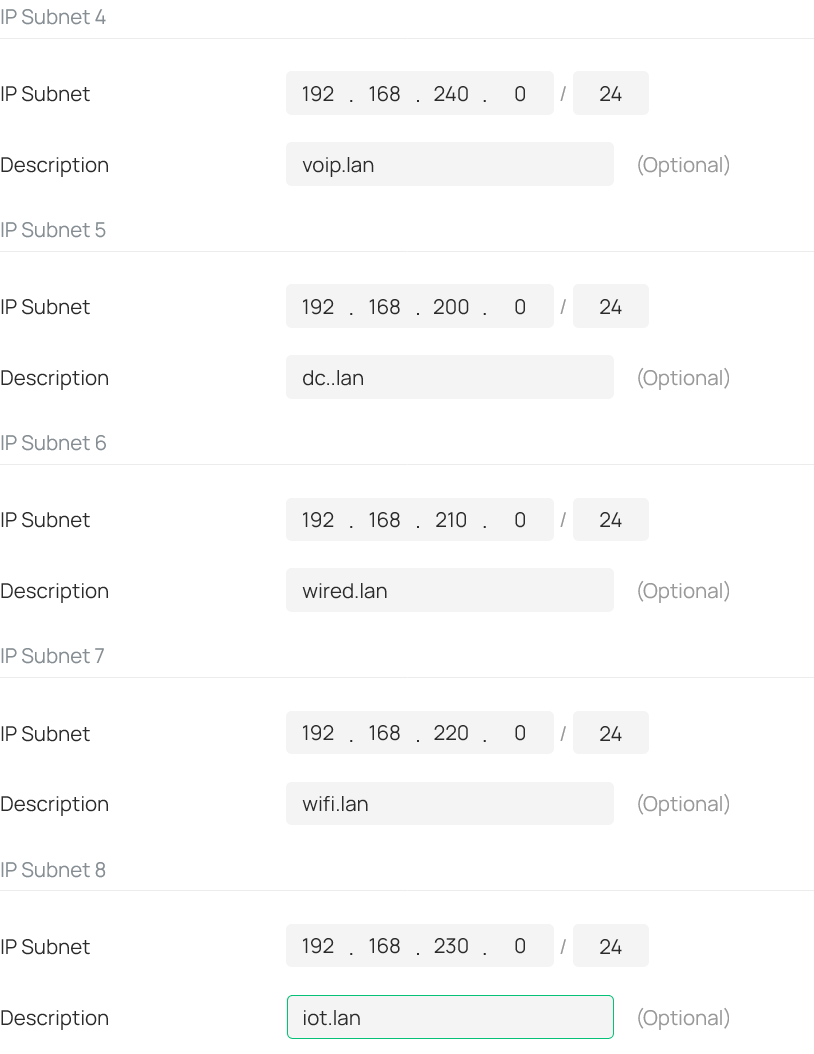
And the other has all other subnets (labeled as !-secure-subnets): 192.168.2x0.0/24. Where x equals 0-4; meaning the 3-th otctet is 200, 210, 220, 230 and 240.
See also attached picture: I then created a deny rule for the gateway-acl (i.e. lan->lan), switch-acl and eap-acl.
All three with the same content as seen in the screenshot from the eap-acl.
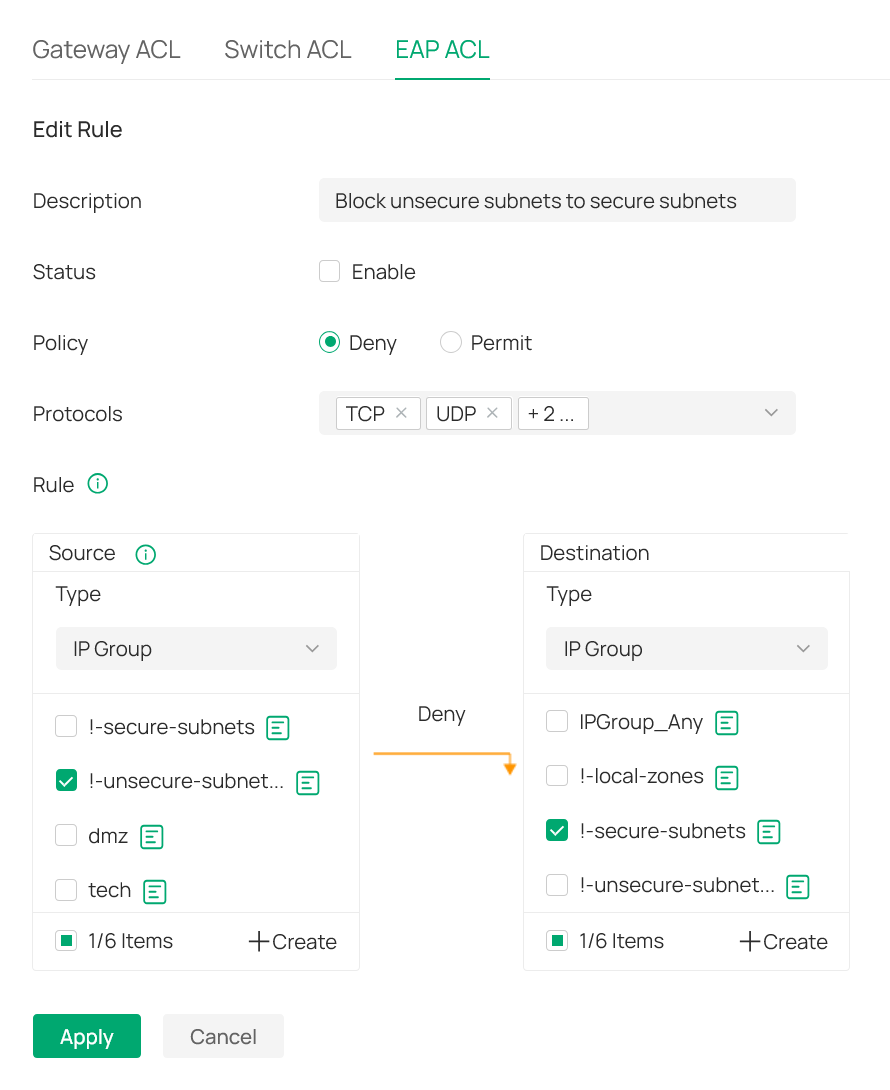
As a result all traffic is blocked?!
What am I overlooking in this setup?
- Copy Link
- Subscribe
- Bookmark
- Report Inappropriate Content
@ITV ,
This is getting complicated. If there are two interfaces for each VLAN, then an ACL is needed for each interface. A deny rule is needed to prevent the VLAN(s) from accessing other VLANs. One rule should be sufficient to block traffic while two rules are needed to allow traffic. If one of the interfaces is on a non-Omada device, then you will have to figure out the needed configuration.
- Copy Link
- Report Inappropriate Content
Information
Helpful: 0
Views: 112
Replies: 11
Voters 0
No one has voted for it yet.
