Firewall rules - how to open smb ports across vlans?
Hello,
It's the second time I ask for directions about setting up smb share across vlans with Omada, because I still haven't figured out this mystery.
I have succeded in opening up port 53 across vlans by defining IP-Port Groups of the target specified ip adress x.x.x.200/32 and making a switch acl rule allow from the networks to the ip-port group. all is working as expected.
If I define a smb nas media server in the same way in an ip-port group with x.x.x.20/32 ports 445 and allow network acces to the device, it will not work.
The allow rule is on top of the other deny rules (the rules that deny traffic between vlans):
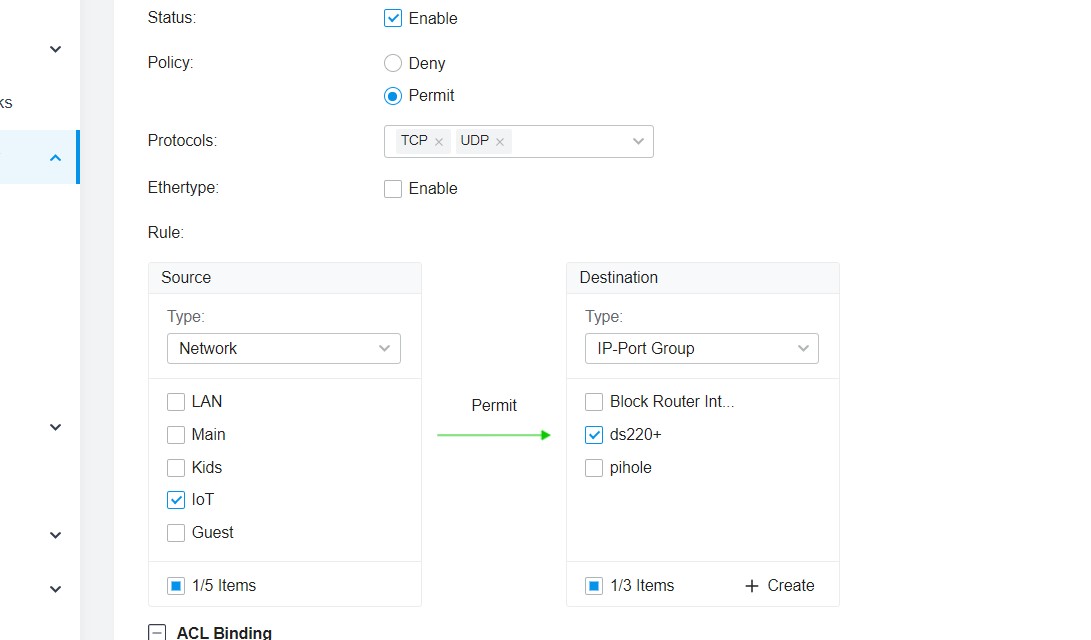
things I have tried.: setting up the ip-port group in the following combinations:
- 445 (permit tcp in the acl - I wouldn't bother with 137-139 as the media server is not a windows machine)
- 445, 137-139 (permit TCP & UDP in the acl)
- 445, 137, 138, 139 (permit TCP & UDP in the acl)
* I wouldn't allow a whole network to the media server, I would make an IP Group with a single IP adress for this rule. I have granted the whole network acces only for testing purposes.
Whatever I do I can't acces the SMB share. If I move the clients in the same subnet smb just works.
Why would this firewall setup permit me to forward a port for pihole server across vlans without problems but it will not allow smb? has anyone succeded in making smb share work across vlans? please do share your firewall switch acl rule, it would be much appreciated.
I kindly ask you to help me understand the firewall rules in Omada.
ps: one thing to mention is that the devices are on different switches and I do not know if this matters because my pihole server can see all clients on any vlans, regardless of the network topology.
