Hacking a valid cert into the EAP controller software
Hacking a valid cert into the EAP controller software
Well I have my own domain name that I use for my home network devices and have used it to put valid certs on them (a pfSense router, an OMV file server, and a couple other gadgets), and thought to myself, "why can't I have a valid certificate on the EAP controller?"
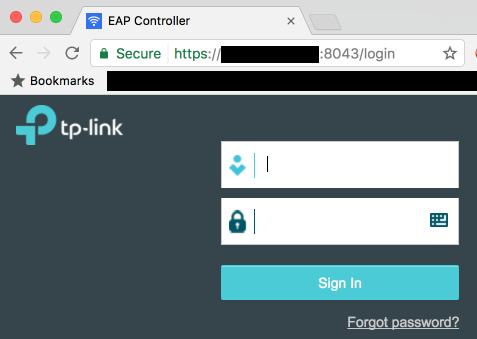
After many hours of poking around with much trial and error, I successfully managed to get the green padlock indicating a valid certificate!
DISCLAIMER: Proceed at your own risk! This worked for me, but I cannot guarantee that this process will not bork your EAP controller, invalidate your warranty, and/or kick an orphaned puppy. Please, think of the puppies.
PREREQUISITES
[*]A domain name that you control DNS for
[*]A way to run the openssl command (either via a handy Linux/Mac box laying around, or an OpenSSL package for Windows on your controller or a handy Windows box)
[*]Full access to your EAP controller box
[*]Depending on your cert provider, an HTTP host you can use for verification
PREPARING
[*]Create a subdomain for your controller under your desired domain name, e.g. "eap.example.com"
[*]If your cert provider requires HTTP verification (e.g. LetsEncrypt), start by pointing this at an HTTP host you have access to, with a very low TTL
PROCESS
[*]Shut down the EAP Controller software
[*]Make a copy of your current keystore (EAP Controller\keystore\eap.keystore) for safekeeping
[*]Generate a private key and CSR:
openssl req -out MYSITE.csr -new -newkey rsa:4096 -nodes -keyout MYSITE.key
[*]Submit your CSR and get the cert from the CA
[*]If your CA uses HTTP verification, once the process is complete change your DNS entry to point to your EAP controller's IP address
[*]Combine your cert and private key into a PKCS#12 key:
openssl pkcs12 -export -in MYSITE.crt -inkey MYSITE.key -name eap -out MYSITE.p12
it is important that the "name" parameter is "eap"!
[*]use an easy-to-remember password, you'll need it a few steps later (then it will be irrelevant)
[*]Make a copy of your current keystore (EAP Controller\keystore\eap.keystore) for safekeeping (you already did that right?)
[*]Delete the eap.keystore file in EAP Controller\keystore
[*]Import your PKCS#12 key into a new keystore:
keytool -importkeystore -deststorepass tplink -destkeystore eap.keystore -srckeystore MYSITE.p12 -srcstoretype PKCS12
enter the password you specified in step 5 when prompted
[*]Restart the EAP Controller software!
When it starts and loads the page, you should still see a certificate error; this is because it loads to https://127.0.0.1 which is never a valid hostname. If you browse to the hostname you created, e.g. https://eap.example.com:8043/ (don't forget the port number) you should now see the valid certificate!
- Copy Link
- Subscribe
- Bookmark
- Report Inappropriate Content
I realise this is an old thread but it is the only one I can find on the topic on replacing the SSL Cert.
I am having the java.security.UnrecoverableKeyException: Cannot recover key error. I have tried importing it using the GUI. This is on an ubuntu based controller.
This is what I have done:
./certbot-auto certonly --standalone --preferred-challenges http -d mydomain.net
openssl pkcs12 -export -inkey /etc/letsencrypt/live/mydomain.net/privkey.pem -in /etc/letsencrypt/live/mydomain.net/cert.pem -certfile /etc/letsencrypt/live/mydomain.net/chain.pem -name eap -out mydomain.p12
delete the existing keystore
keytool -importkeystore -deststorepass tplink -destkeystore /path/to/keystore/eap.keystore -srckeystore mydomain.p12 -srcstoretype PKCS12
tpeap stop
tpeap start
Is there anything obvious. I can't believe nearly a year on this still isn't easy
Thanks
- Copy Link
- Report Inappropriate Content
The password you set in step 5, *must* be tplink.
openssl pkcs12 -export -in MYSITE.crt -inkey [I]MYSITE.key -name eap -out [I]MYSITE.p12[/I][/I]
[I][I]it is important that the "name" parameter is "eap"![/I][/I]
[*][I][I]use an easy-to-remember password, you'll need it a few steps later (then it will be irrelevant)[/I][/I]
- Copy Link
- Report Inappropriate Content
I just successfully used an LE cert on my controller. Here is what I did.
First I created a script that stops the controller, builds a new keystore and then starts the server. You can get the script here:
https://pastebin.com/raw/U1zYQGHe
Then I generate the new cert using acme.sh (https://acme.sh) and reference my script (reloadEAP.sh) similar to this:
./acme.sh --issue --dns dns_cf -d eap.example.com --reloadcmd /root/.acme.sh/reloadEAP.sh
If you want acme.sh to setup a cron job to automatically renew the cert and automatically inject it into the EAP controller just run this command:
./acme.sh --install
Obviously you will need to alter the paths in the script and find the right command line options for generating a cert with acme.sh for your environment. You don't have to use acme.sh, my relaodEAP.sh script could be adapted to work with any cert you want. I'm mostly using the steps I found in this thread only I added the password to the command lines so it can be run without user interaction.
Hope this helps someone.
- Copy Link
- Report Inappropriate Content
See this recipe for an easy way to permanently install an own SSL certificate in Omada Controller:
https://community.tp-link.com/en/business/forum/topic/150083
- Copy Link
- Report Inappropriate Content
- Copy Link
- Report Inappropriate Content
- Copy Link
- Report Inappropriate Content
Information
Helpful: 0
Views: 12542
Replies: 16
Voters 0
No one has voted for it yet.
