Solution Optimizing WireGuard VPN Client Connectivity on the M8550
This Article Applies to:
M8550(EU/US)_V1.0/1.6
Hi All,
To address critical reliability and performance issues with the WireGuard VPN client on the M8550, our engineering team has developed a targeted firmware update. This update resolves configuration parsing errors, enhances connection stability, and improves traffic routing efficiency.
It is recommended to install this beta firmware if you happen to experience the following situations:
- Configuration File Import error: Users are unable to import WireGuard VPN configuration files due to parsing errors or unsupported parameters.
- Connection Failures: After the configuration file is imported successfully, the VPN tunnel fails to establish a stable connection.
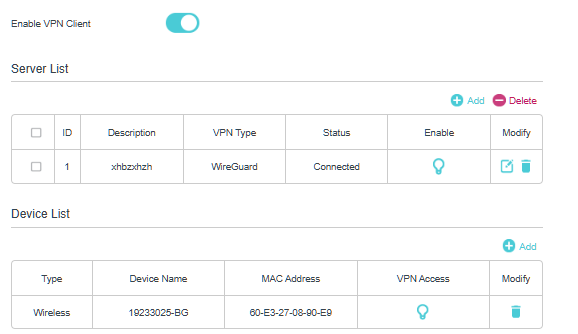
- Traffic Routing Issues: VPN Client status may display "connected", but VPN traffic can't pass properly between the client and the remote WireGuard VPN server.
Firmware Download Link:
| M8550(US)_V1.6 | 1.2.0_3.0.0_Build_20260121_Beta |
| M8550(EU)_V1.0 | 1.3.0_3.0.0_Build_20260126_Beta |
Update Notice:
- Please be sure you have read the Beta Test Agreement before upgrading the Pre-release firmware!
- How to upgrade firmware of TP-Link 5G Mobile Wi-Fi
- The Beta firmware could revert to the official 1.20/1.3.0 firmware versions.
Please feel free to comment below whether the 1.2.0 firmware helps to ensure stable VPN connectivity.
If you still experience any issues with WireGuard VPN Connection on M8550, please feel free to comment below and include a detailed description of the behavior and as much information as possible regarding the specific conditions that seem to trigger it.
Your input helps us continue to improve and provide the best possible products and support.