DHCP for VLAN not working
After performing firmware updates on for the Omada Controller (OC200), router, and switches, I started having problems with my VLAN behavior.
I deleted everything and created a new VLAN. Wired clients to the VLAN are not getting IP address assigned. Even when I staticlly assign the IP address in the range of the VLAN they fail to get a response from the DHCP server.
My default(1) lan DHCP server is working correclty both wired and via the EAP. It's just the VLAN that's not working. I didn't setup any ACL's, I've reviewed the Port settings.
I must be missing something. What should I be looking at to get this working?
- Copy Link
- Subscribe
- Bookmark
- Report Inappropriate Content
Thanks for reaching out to TP-Link Business Forums.
May I confirm what's the current version of your controller?
This seems to be related to the configuration. After setting up the VLAN, did you assign it to a certain port only?
You can refer to this How to configure VLAN with Omada Network v6 | Omada Network Support
- Copy Link
- Report Inappropriate Content
Make sure you have trunked all ports between gateway and EAP to carry the untagged 1st vlan and the tagged 2nd, make sure you set the SSID vlan tag correctly, and this should just work
- Copy Link
- Report Inappropriate Content
Thanks for the reply. The versions are below. The problem isn't with the EAP, that only provides DHCP to the default(1) lan which is still working. The problem is with a wired only VLAN. Before upgrading the router from 2.2.6, the vlan setup was functioning correctly. After the upgrade is when the problems started. I did remove the vlan, leaving only the default in place, and rebuilt everything, and I did follow the guide in the link you provided.
Further reading of various threads, I found some mention that resetting all devices to factory default and starting completely over resolved their problems. Unless I have another option I'll have to try that next, but it takes a bit more planning.
| MODEL | VERSION |
| EAP225-Outdoor(US) v1.0 | 5.0.5 Build 20210604 Rel. 51118 |
| ER605 v2.0 | 2.3.3 Build 20251029 Rel.18054 |
| SG2210MP v4.20 | 4.20.20 Build 20260310 Rel.10715 |
| ES205GP v1.0 | 1.0.3 Build 20250609 Rel.74647 |
| SG3428X v1.30 | 1.30.19 Build 20260310 Rel.11233 |
| SG2210MP v5.0 | 5.0.17 Build 20260310 Rel.10715 |
| EAP660 HD(US) v1.0 | 1.4.3 Build 20250714 Rel. 64055 |
- Copy Link
- Report Inappropriate Content
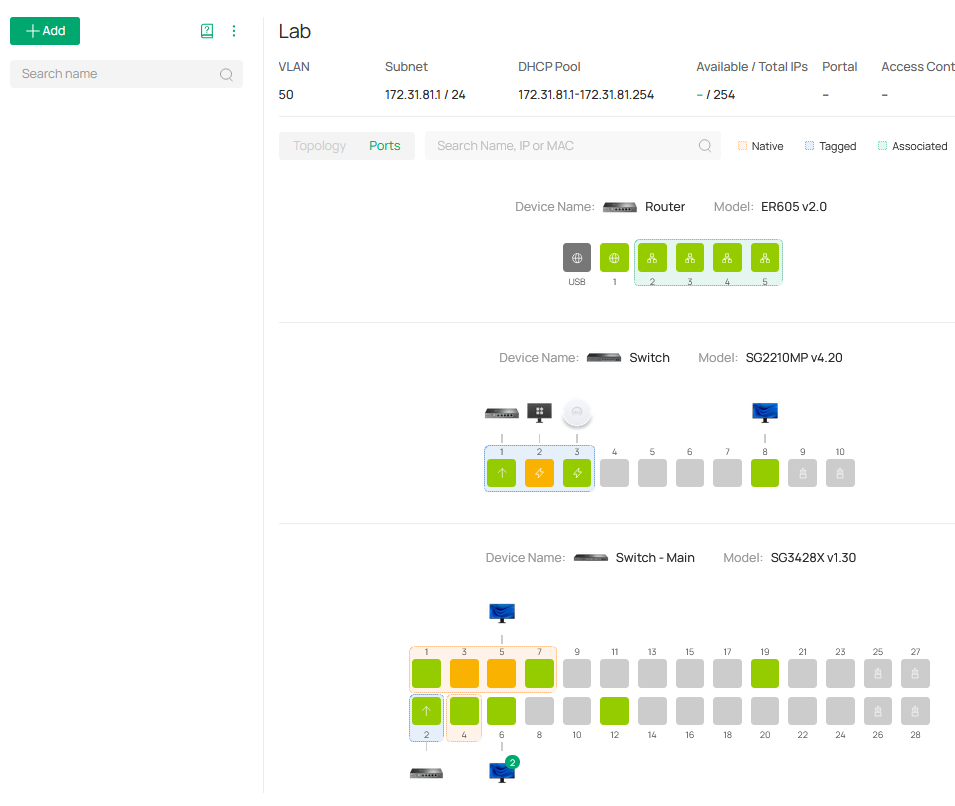
In the screen shot, you can see all the ports (blue highlight) are trunked and the (red highlight) are the ports for the devices that are in the vlan.
- Copy Link
- Report Inappropriate Content
Today I did a full factory reset on all the gear. In reconfiguring my network I discovered what I think is the problem.
I've discovered a routing behavior that did not exist in the 2.2.6 firmware for the router. The setup involves a default LAN, a VLAN, and a VPN Client connection. Summary: with the VPN active DHCP does not work in the VLAN, routing isn't working as expected between the different subnets.
LAN uses subnet A
VLAN uses subnet B
VPN routes to subnet C and supports routing to subnet B
Without the VPN active:
A pings B
B pings A
B devices DHCP is works as expected.
VPN configuration set with Local Network type including Default(A) and VLAN(B)
A pings B
A cannot ping C
B devices DHCP stops working.
VPN configuration set with Local Network type including only VLAN(B)
A pings B
A cannot ping C
B DHCP does not work.
VPN configuration set with Local Network type to custom using IP B/24
A pings B
A cannot ping C
B DHCP does not work
VPN configuration set with Local Network type to custom using IP B/24 and A/24
A cannot ping B
A pings C
B DHCP does not work
What worked in version 2.2.6
VPN configuration set with Local Network type including LAN(A) and VLAN(B)
A pings B
A pings C
B pings C
DHCP in B works.
I am unable to find a configuration, using static routes or other settings that allows routing shown in that last configuration.
I also feel this was the problem I thought I was having with DHCP first posted. I would have seen this disabling the VPN without the need to reset to factory defaults.
- Copy Link
- Report Inappropriate Content
Information
Helpful: 0
Views: 202
Replies: 5
Voters 0
No one has voted for it yet.
