HTTPd "local" admin server is binding to both LAN and WAN interfaces
So, when using Advanced IP Scanner v2 to scan my entire home network, I noticed that in the physical DMZ network we have, the ER7206 was offering an HTTP(S) service.
Being curious, I took a look and yes, the local admin pages are fully accessible on the WAN side of the network I'm running as well as the LAN side.
Clearly the httpd service is configured to bind to all interfaces when it should not be doing so.
Here's the LAN side admin URL in the browser which is fine.

I wasn't expecting the httpd server to respond but it does on the WAN side of the network.

Here's the WAN IP address DHCP assignment from our primary router.

I have run a router as a secondary router/firewall ever since I found out that our ISP has a back door built into the firmware of their router which we MUST use. The ER7206 is the latest router I've put into the network replacing the old router that broke. The ER7206 is therefore being used to create a small DMZ network that our ISP can see with guest Wi-Fi on it, then, behind the ER7206, our main network exists.
By doing this, our main network is fully protected from prying eyes. However, I wasn't expecting the httpd to be providing access to the admin area on the WAN side of things at all and I view this as a security risk.
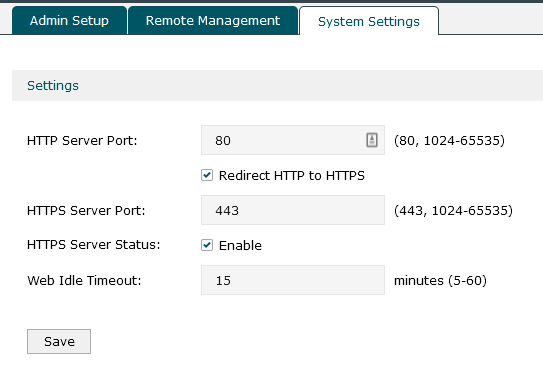
As you can see from the next screenshots, remote admin is off...

HTTP admin is configured to redirect to HTTPS.
There's no way to specify which side of the LAN/WAN the httpd should bind and I'd expect it to default to LAN binding only but it seems it is binding to every available interface.
I know the router is password protected but as a security issue, the admin area interface shouldn't really be binding to the WAN side of the router at all.
Is this a bug or an issue with my configuration? Is there a checkbox I'm missing that I need to change to fix this or would it require a firmware update to change the network binding details for the router?
Thanks
Paul



